Information Security
Information Security Policy
The Group positions information security and cyber security as management issues of the utmost importance. As such, we are aware of our societal duty to protect the information assets in our possession, including those of our clients, from various security threats, and through the compliance of our officers and employees with the following Information Security Policy we have established, we make every effort to maintain and enhance the confidentiality, integrity, and availability of our information assets.
Please see the following for details:
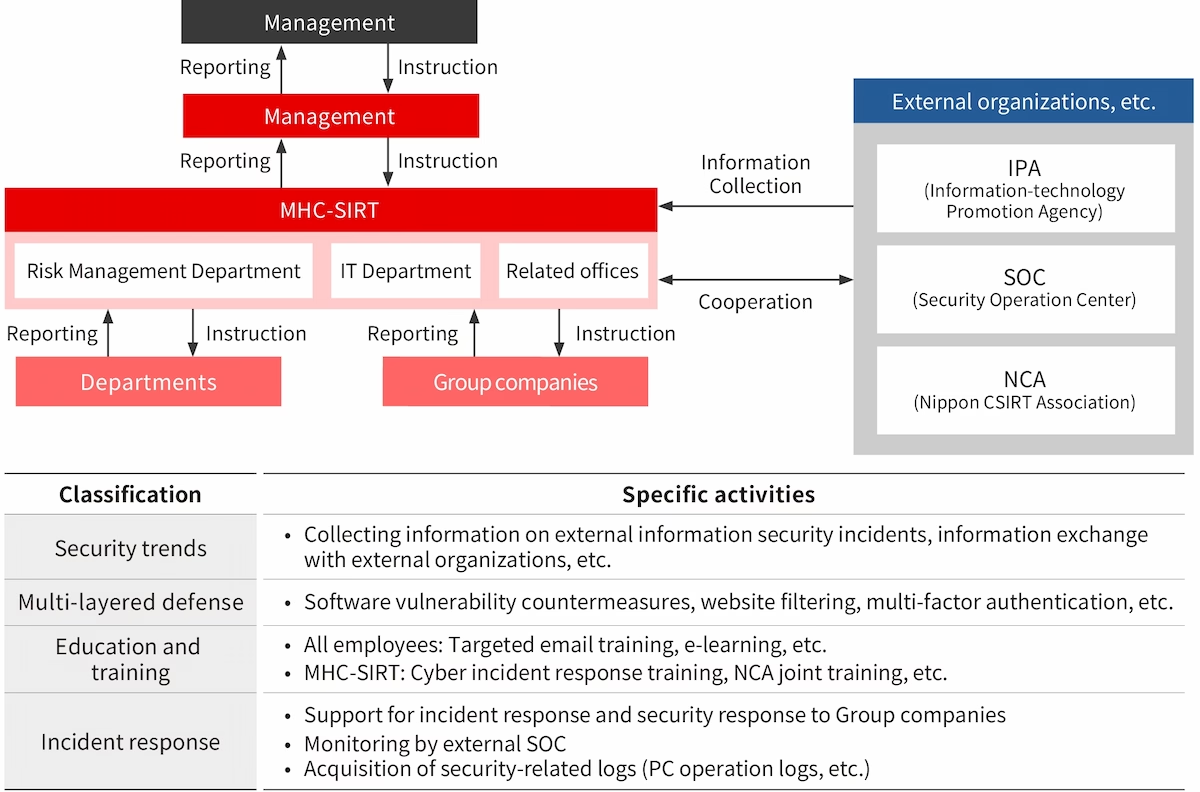
Information security organization
To protect all of its information assets from various security threats, the Group strives to establish an effective information security management framework and rules. We have established a cross-organizational team, the MHC-SIRT (Security Incident Response Team) led by the Head of the Risk Management Division (CISO) who is a Managing Executive Officer, which is responsible for preventing cyberattacks, conducting periodic in-house education and training, and examining responses and investigating causes when incidents occur. In addition, each office has an Information Security Manager and a person in charge of information security assigned, constituting an information security management framework on a Company-wide basis.
Security trends
The MHC-SIRT collects, assesses, and shares information about cyber-attacks that occur in Japan and overseas, vulnerabilities, etc. on a daily basis and takes countermeasures swiftly and appropriately, with the cooperation of external institutions specialized in security.
Multi-layered defense
The Company has taken multi-layered technical measures to prepare for cyber-attacks, such as monitoring of device behaviors using EDR,*1 software vulnerability countermeasures, website filtering, and multi-factor authentication. For public websites that manage personal information and other important information, the Company has taken technical measures such as implementing WAF*2 and a tamper detection system. The Company also regularly conducts vulnerability assessments using an assessment service at least once a year in addition to the time of developing the websites, and takes corrective measures in accordance with the seriousness of vulnerabilities.
To prepare for human errors, the Company has in place a system to prevent email errors, which encourages self-checks and automatically password-protect attached files when sending emails externally. Furthermore, files that include high-risk information are automatically detected by a system and cannot be sent before being double-checked by a manager.
- *1Endpoint detection and response: A system that monitors suspicious behaviors of and attacks to PCs and servers for the purpose of taking swift response
- *2Web application firewall: A security measure to protect web applications from malicious attacks
Education and training
The Company conducts e-learning education on information security and cybersecurity for all officers and employees every year. To ensure information security management, information security training is conducted and a written oath on security rules that must be complied with by officers and employees who engage in operations is collected when employees enter the Company. Learning contents and other materials of the Company are shared with its Group companies, and the entire Group is actively working on information security education. In addition, as education on targeted emails and phishing emails, the Group conducts targeted email training every year, in which attack simulation emails are actually sent to officers and employees to increase their sensitivity to security.
The MHC-SIRT conducts a drill based on multiple scenarios of ransomware infections, unauthorized access, etc. and a joint drill within the Group once a year. The Company also participates in an nationwide joint CSIRT drill hosted by the Nippon CSIRT Association and the National Center of Incident Readiness and Strategy for Cybersecurity every year to increase the effectiveness of our response to cyberattacks.
Incident response
The Company has in place escalation rules and incident response procedures to prepare for information security and other incidents. In times of emergency, the MHC-SIRT takes the lead in initial response, identification of the scope of impact, recovery, recurrence prevention measures, etc. Serious incidents are reported to the Head of the Risk Management Division (CISO) and management takes the lead in responding to the incidents.
In addition, the Company conducts security monitoring using an external security operation center (SOC) on a 24/7 basis, so that the Company can prevent the spread of damage and recover early on such as by isolating affected devices when an anomaly is detected.
Information security management for partner companies
The Company has in place procedures to select and manage external business partners and assesses the status of information security measures, etc. at business partners based on information security requirements when outsourcing operations. The status of management at business partners is checked and examined once a year.
Third-party assessment and certification
A department of the Company (the Public Business Department) underwent assessment by the Japan Quality Assurance Organization (JQA) and acquired ISMS certification under ISO/IEC27001.
